In a Nutshell: Most consumers think of credit card information as the most valuable personal data to cyber thieves. But strategies put in place by card issuers to lock a credit card the instant fraud is suspected makes it a valuable commodity for only a brief period of time. A recent study by Trustwave found that medical records and personal identifiable information — like Social Security and driver’s license numbers, gender, race/ethnicity, and birth date — are more valuable to cyber thieves because they are harder to change or freeze. The study found that credit card data could be worth as little as 5 cents per file on the dark web black market, whereas medical records could command $10 each. Trustwave’s data security and POS solutions have helped shape industry regulations that are used globally by businesses in all industries. //
A shopper’s biggest dilemma when buying a gallon of milk at the grocery store is whether they’ll be able to finish a whole gallon before it expires. But those three seconds between the time you swipe your card for payment and sign the screen or receipt to complete the transaction are filled with more action than you may realize.
Americans’ preference for using cash is decreasing yearly, while digital forms of payment — most notably debit and credit cards — continue to grow. Card issuers are relying on the speed and dependability of these forms of payment to keep their market share growing.
When you swipe your card, its information is sent via the internet to the merchant’s bank. The bank then sends the information to the credit card network for authentication, which sends the approval to the bank that issues the card. The issuing bank then sends a confirmation of funds through the same channels in reverse order, which culminates in a receipt to mark the end the transaction.
Not bad for three seconds of work.
But in those three seconds, your personal information — credit card number and expiration date, billing address, CVV security code, and payment amount — floats around the atmosphere and relies on third-party security measures to keep it safe.
Shoppers’ lack of interest in what happens during those three seconds reveals the level of trust they have in the security measures taking place. The Personal Card Industry (PCI) maintains a strict set of standards for merchants accepting electronic payments. Trustwave, an industry-leading managed security services firm, helped shape those standards.
As a global leader in handling the management of threats, vulnerability, and compliance, Trustwave is at the forefront of research on trends and topics critical to the security industry. The latest study released by the firm is the Value of Data Report.
The research looks at the value placed on stolen personal data available for sale on the dark web. Personal information can be pilfered through many avenues — including mass credit card security breaches or via lapses in point of sale (POS) security systems during checkout.

One of the study’s most interesting findings is that the going rate for ill-gotten individual credit card data files can range in value from 5 cents to $18 each on the dark web black market.
“When there’s a large credit card data breach, the thieves have dump files where they put all the data — they’ll have the cards’ PIN numbers, the expiration dates, and the name on the card,” said Shawn Kanady, Principal Security Consultant at Trustwave. “They sell this information in blocks. As time goes on, the value of these records depreciates because people are reporting fraud or having their cards changed.”
The 17-page document also shows that credit card data is 60 times more valuable to the card issuers than it is to thieves.
“A security breach hurts their brand and gets them fined,” Shawn said. “Those costs can stretch way beyond that up-front bill. The investigation costs and long-term impact can be crippling.”
The study also found that personal card data has the highest black-market value in the US, the UK, and Australia, but it is not as valuable in Canada and Japan because higher security standards make the data harder to reuse.
“These guys stealing the card information run their businesses like Fortune 500 companies,” Shawn said. “They know their data and what it’s worth”
Financial Data Not the Only Information at Risk
The data protection and recovery industry is expected to be worth $14.1 billion annually by 2025 due to security concerns around data storage in the cloud.
Increased global security standards — including the European Commission’s General Data Protection Regulation (GDPR) — are meant to impose similar rules on data storage as the standards PCI sets for credit card acceptance.
Personal Identifiable Information has Greatest Value in the US
Personal Identifiable Information (PII) can include something as simple as your name or as complex as your Social Security and driver’s license numbers. It also comprises your citizenship, legal status, gender, race/ethnicity, birth date, and telephone numbers.
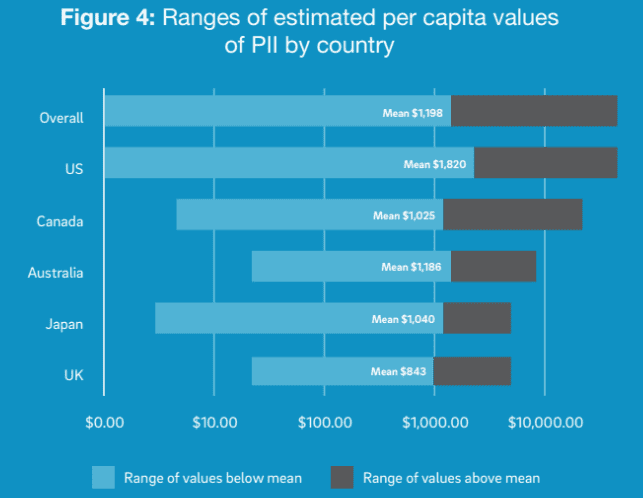
The graph shows ranges of estimated per capita values of PII by country from Trustwave’s Value of Data Report.
If stolen, this information can be used to take out lines of credit in your name or gain access and exploit existing credit lines.
The study found that US professionals value their PII at $1,820 — more than twice the value assessed by UK professionals ($843) and higher than Canada ($1,025), Australia ($1,186), and Japan ($1,040).
The disparity is attributed to the higher security standards used for storing US data, making it harder to steal. When Europe’s GDPR begins imposing stiff penalties for non-compliance in 2018, the value of the UK PII is expected to increase dramatically.
Data risk vigilance, a measure of the efforts put in place to care for data, is highest among Canadian firms and lowest among Australian businesses, while US vigilance came a close second behind Canada, followed by the UK and Japan.
Patient Data is the Most Rigorously Assessed
Most consumers fear having their credit card information stolen more than other personal data. But, to data thieves, medical records are more valuable than credit card numbers.
The data most stolen from aging hospital computer systems includes birth dates, insurance policy numbers, diagnosis codes, and billing information.
Hackers use the data to create fake IDs to purchase medical equipment or drugs for resale. Patient numbers can be combined with false healthcare provider numbers to file made-up claims with insurers.
A single stolen health credential can sell for $10, far more than the average single credit card file.
Making secure storage more of an issue is the move toward Electronic Health Records (EHR). Electronically stored health information is taking the place of traditional hard copy patient charts because it can be shared across different healthcare settings. That accessibility makes it a prime target for thieves.
Trustwave’s study shows that 85% of US organizations with patients as their prime data subject carry out regular, comprehensive risk assessments in part due to tight regulation through the Health Insurance Portability and Accountability Act (HIPAA).
How Trustwave Protects Consumers and Brands
Consumers trust brands and businesses to protect their personal financial information when making purchases online and in person. PCI compliance for POS systems is designed to maintain that trust and hold merchants to the highest security standards.
“Trustwave was with PCI from the get-go as one of the companies that helped build the regulations,” Shawn said. “There are lots of requirements — like firewalls, log management, and many other things just to be PCI compliant and accept credit cards.”
Adding Manpower to Your Software Platform
Shawn said that just having the proper software in place isn’t enough to ensure safe transactions at the register.
“A lot of companies are putting in the required pieces of hardware and software, but they don’t have the processes or people to manage them,” he said. “It turns into a set-it-and-forget-it sort of thing. That doesn’t work for security.”
Most large corporations have the budgets to employ a security and compliance team to work with their IT department. Shawn said that Trustwave works with those clients, but also has services tailored to smaller firms that need help.
“Small- and medium-sized businesses often don’t have an IT department,” he said. “If they do, they usually don’t have a security side of the department. There isn’t enough time to do both jobs in one department. We can come in and manage your security for you, or work with your IT department to meet your needs.”
Guiding PCI Compliance from Start to Finish
Trustwave’s POS and PCI compliance systems have the tools and manpower businesses need to gain operational peace of mind. Its experts can install and maintain new security software or work within an existing framework to gain compliance.
“Once you have your system in place, a Quality Security Assessor (QSA) has to go through your system and do an assessment,” Shawn said. “We do all of that. We offer everything POS merchants need to get going with credit cards with a 24/7 monitored environment.”
On the Forefront of PCI Compliance Since the Beginning
Business owners spend years cultivating a following for their brand — and their work can be undone by hackers in mere seconds.
Trustwave has a history of protecting data and providing POS security solutions for businesses around the globe. The firm employs specialists who are adept at staying ahead of the trends in methods that data thieves use to steal valuable information.
“Hackers are getting stronger and more sophisticated and are utilizing multithreat techniques,” Shawn said. “It’s not just an email that you can delete because you know it’s a phishing email. They’re constantly finding new ways to stay ahead of people.”
Advertiser Disclosure
CardRates.com is a free online resource that offers valuable content and comparison services to users. To keep this resource 100% free, we receive compensation for referrals for many of the offers listed on the site. Along with key review factors, this compensation may impact how and where products appear across CardRates.com (including, for example, the order in which they appear). CardRates.com does not include the entire universe of available offers. Editorial opinions expressed on the site are strictly our own and are not provided, endorsed, or approved by advertisers.

![7 Best Major Credit Cards ([updated_month_year]) 7 Best Major Credit Cards ([updated_month_year])](https://www.cardrates.com/images/uploads/2019/10/Best-Major-Credit-Cards-Feta.jpg?width=158&height=120&fit=crop)
![9 Best Study Abroad Credit Cards for Students ([updated_month_year]) 9 Best Study Abroad Credit Cards for Students ([updated_month_year])](https://www.cardrates.com/images/uploads/2018/06/Best-Study-Abroad-Credit-Cards.jpg?width=158&height=120&fit=crop)
![How to Get a Black Card – American Express® Requirements ([updated_month_year]) How to Get a Black Card – American Express® Requirements ([updated_month_year])](https://www.cardrates.com/images/uploads/2016/03/How-to-Get-a-Black-Card-2--1.jpg?width=158&height=120&fit=crop)



